Android and iOS Smartphones and Tablets Monitoring
Monitor mobile phone usage
- Track calls and text messages
- Monitor, block, and limit SMS
- Check contacts and calendar
Follow online activity
- Monitor browsing history
- Block websites and apps
- Monitor social media and chats
Control the device remotely
- Use SMS commands to control
- Lock and wipe the device remotely
- Keep track of location and route history
Why Parental Controls Are Essential
Most threats children face today are closely associated with the use of mobile devices and the Internet. Our cell phone monitoring software helps parents avert all these dangers in the making and protects your little ones. Because our software is not linked to any cell phone carrier, you can benefit from it even outside the US or Canada as Pumpic app is available in different countries around the globe. Install the app on your kids’ phones and rest assured they are safe wherever they or you go.
Pumpic is compatible with the two most wide-spread mobile operational systems – iOS and Android. As more and more parents choose Apple devices for their children, iPad, iPod and, of course, iPhone parental control solutions became a genuine necessity. Pumpic iOS monitoring works via iCloud and doesn't require jailbreak or app installation. In turn, the best manner to fix up comprehensive Android parental control on smartphones and tablets is by installing a password-protected application. Although a wide range of features is available without root, it might be needed for even broader monitoring functionality.
Regardless which operational system the device you need to monitor runs on, Pumpic is a reliable child tracking solution that each concerned parent should consider using. Keep your eyes open with the Pumpic parental controls.
Useful Features for Every Careful Parent
- Monitor SMS and MMS
- Monitor Calls History
- View Calendar
- View Contacts
- View Emails
- View Photos
- View Videos
- Remote Control Panel
- Control Browser
- Control Applications
- View Bookmarks
- View Notes
- Block Device
- Location Tracking
- Geo-fences
- Keylogger
- Monitor WhatsApp
- Monitor Skype
- Monitor Facebook IM
- Monitor Viber
- Monitor Instagram
- Monitor Kik
- Monitor Snapchat
- SMS Commands
 View All Features
View All Features
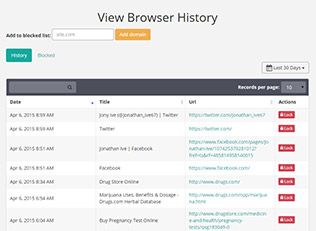
Easy-to-Use Control Panel
Right after installing Pumpic mobile monitoring, all the data from the target mobile phone will be sent to your Control Panel. You can access it from any browser and any device, including PCs, smartphones, and tablets. In Control Panel, you can not only monitor the information but also set parent restrictions and block some activities on your child’s phone remotely.
Trusted by Over 10,000 Customers Worldwide:
How It Works

Pick a subscription plan
Visit our Store, check out available subscription plans and choose the one that meets your expectations and monitoring preferences. After you submit a payment, you will receive an email with setup instructions.
Set up
Pumpic app setup process will take you no longer than 5 minutes. Follow the guidelines in the email to complete the setup. Note that physical access to the Android target device is required before installation. It may be as well needed to launch iOS solution (iCloud monitoring) (check/adjust settings, turn Backup on).

Track remotely
To see the data from the target device, access your Control Panel via Pumpic or Mobile App for iOS & Android (has a limited amount of features!). In the Control Panel, you can view logs, media files, location history, set restrictions, manage your devices and subscriptions.